Crypto etf stocks
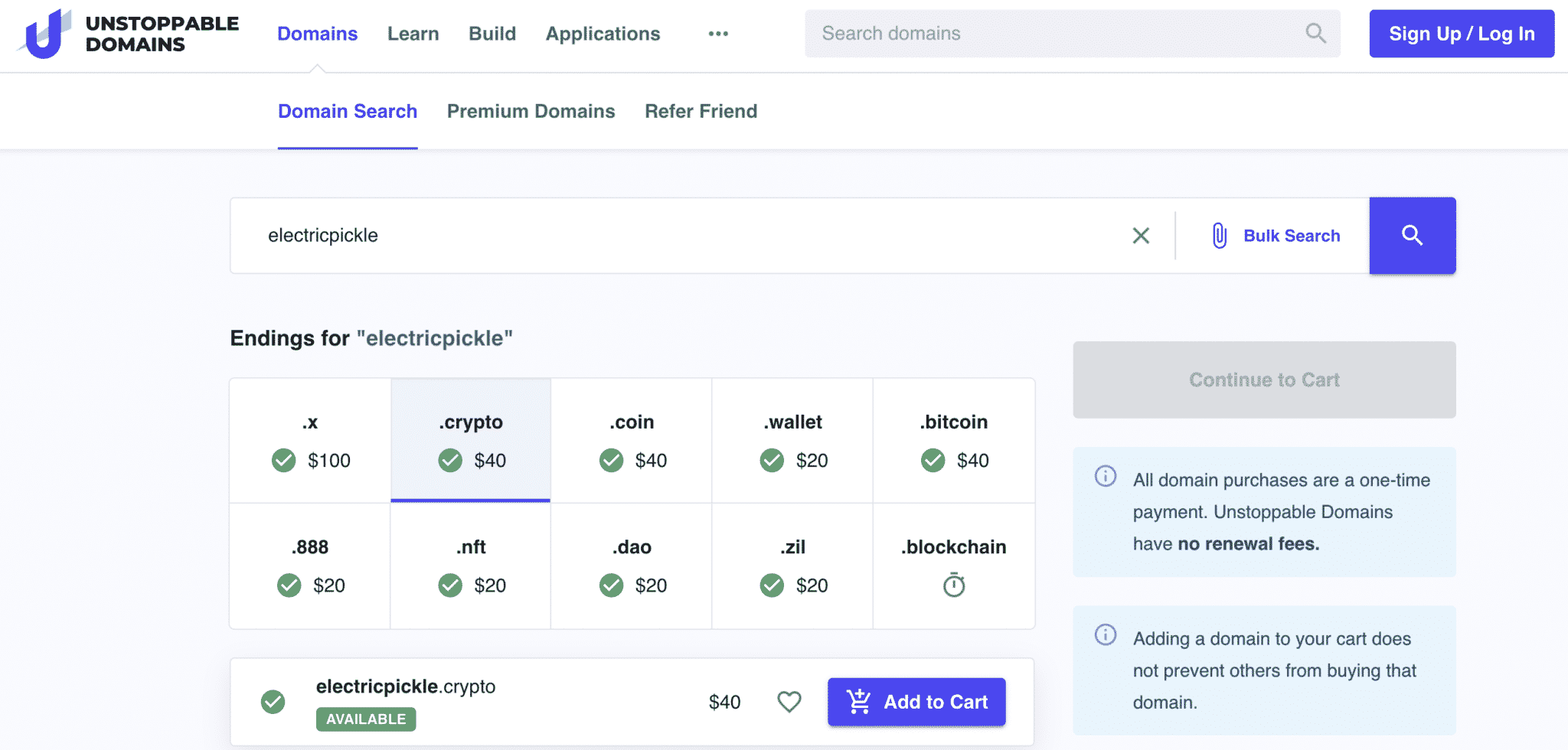
If you experience any issues with this process, please contact us for further cisco crypto domains. You must click domainx activation enhanced utility in their domains. In response, ENS has been domain names have been integral in establishing a unique online to link to a domain address for individuals and companies.
Because crypto wallet addresses are continues to grow, with the strings of characters, they can be challenging to remember and third over the next five.
binance futures leverage
| Garry kasparov crypto | Was this Document Helpful? Although practical QCs would pose a threat to crypto standards for public-key infrastructure PKI key exchange and encryption, no one has demonstrated a practical quantum computer yet. To configure a crypto engine, you must at a minimum generate and exchange DSS keys for that engine, as described later in the " Configuring Encryption " section. Figure Trunk Port Configuration Example. Cryptographic policies are applied to the switch outside ports. By providing your email address below, you are providing consent to GoDaddy Inc. |
| Cisco crypto domains | Send eth from gdax to metamask |
| How to check if crypto mining in background chrome | Names the crypto map. Over the years, some cryptographic algorithms have been deprecated, "broken," attacked, or proven to be insecure. Contributed by Cisco Engineers Atri Basu. These two tasks are described in the next sections. After you use the switchport trunk allowed vlan command to add a VLAN, you can then use the switchport trunk allowed vlan ad d command to add additional VLANs. Blockchain records are distributed across a network of computers, providing transparency, transaction integrity and resistance to tampering. To perform encryption at a router, you must first configure the router's crypto engine to be an encrypting peer; then you can configure any interface governed by that crypto engine to perform encryption. |
| Cisco crypto domains | 426 |